Encryption in Medieval Times
Most of us today think of encryption as a modern concept, dependent on powerful computers and complex mathematics to keep information safe from prying eyes.  The notion of coded messages is, however, a far older idea.
The notion of coded messages is, however, a far older idea.
One of the earliest recorded uses of encryption techniques is the Caesar Cipher, so named because of its use by Julius Caesar to send secret messages during his military campaigns. It is a simple alphabetic substitution cipher in which the receiver need only know the sender’s offset to decode the message. Julius Caesar was known to use an offset of 3, meaning that the letter “D” would be substituted for “A” in the coded message. One would use the same offset, or key, for the entire message.
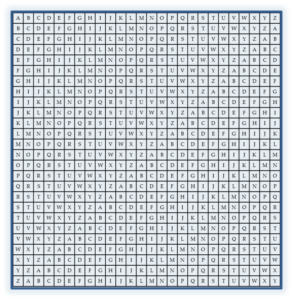
Sometime around 800 CE, an Arab mathematician writing about code breaking techniques included references to polyalphabetic ciphers. These ciphers use a table such as the one to the right and the key is the letter of the row or column used for the encryption.
With such a scheme, one can conceivably vary the key multiple times within a message. Though the polyalphabetic cipher is mathematically no more secure than a simple substitution cipher, using multiple keys can require more effort on the part of a code breaker using pattern analysis and similar decoding techniques.
In Second Son, Alfred uses the Caesar Cipher to encode a message to his grandfather. Later, his lifelong devotion to expanding the library founded by his grandfather has introduced him to the idea of polyalphabetic substitution.
Bust of Julius Caesar image credit: Copyright: artsy / 123RF Stock Photo</span.
